Associate of Applied Science
66
Sioux City
Online
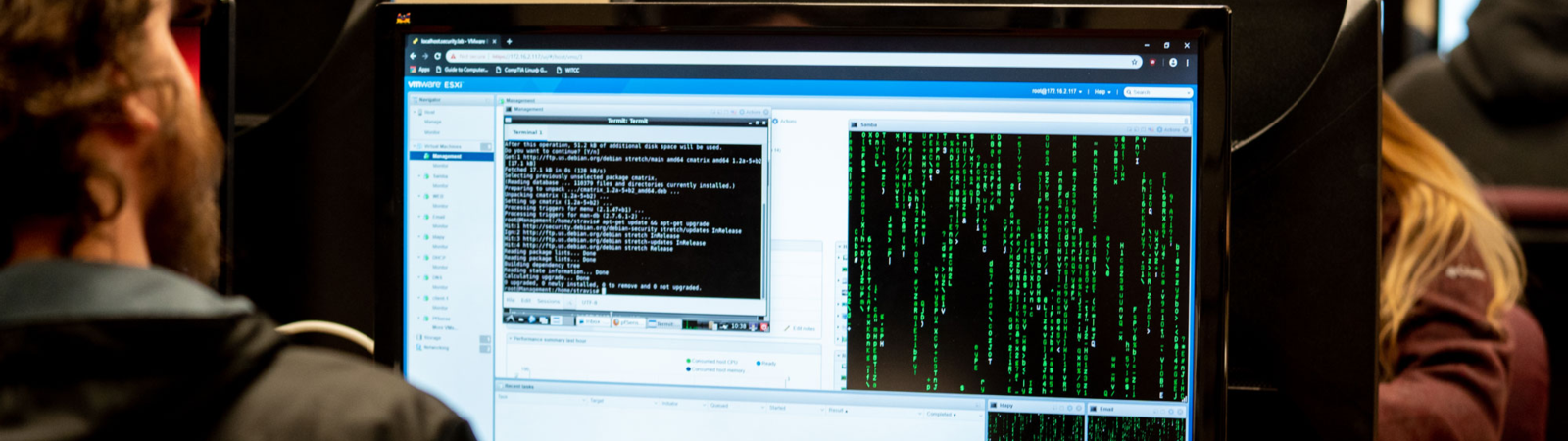
This program is designed to fill a critical and growing need for cyber security personnel in the public and private sector. Upon completion, you will be capable of investigating computer crimes, properly seizing and recovering computer evidence, and aiding in the prosecution of cyber criminals.
Skills learned enable you to investigate computer crimes, develop security best practices, and secure network infrastructure.
To combat computer related crime, you will also understand counter measures against hacking, spam, and computer viruses through network intrusion detection and evidence gathering. The work of cyber crime investigators often aids in criminal investigations, supports lawsuits, and prevents future attacks.
Courses help individuals develop an understanding of identity theft, networking, incident response, exploitation, social engineering, black hat/gray hat hacking, and network security. Counter measures against hacking, spam, and computer viruses through cyber sleuthing and evidence gathering are used to combat cyber crimes.
Careers in Cyber Security & Digital Crime can be found in local, regional, and national sectors such as governmental agencies, law enforcement and security, homeland security, law firms, businesses: human resources and information technologies, insurance agencies and companies, banks and credit card companies, health services, and educational systems.
Professional opportunities are plentiful in this innovative and expanding career.
Meet Your Advisor
Career Navigator
colleen.clifford@witcc.edu
Call 712.317.3126
Sioux City Campus, Admissions
Book Appointment